TL;DR — Quick Summary
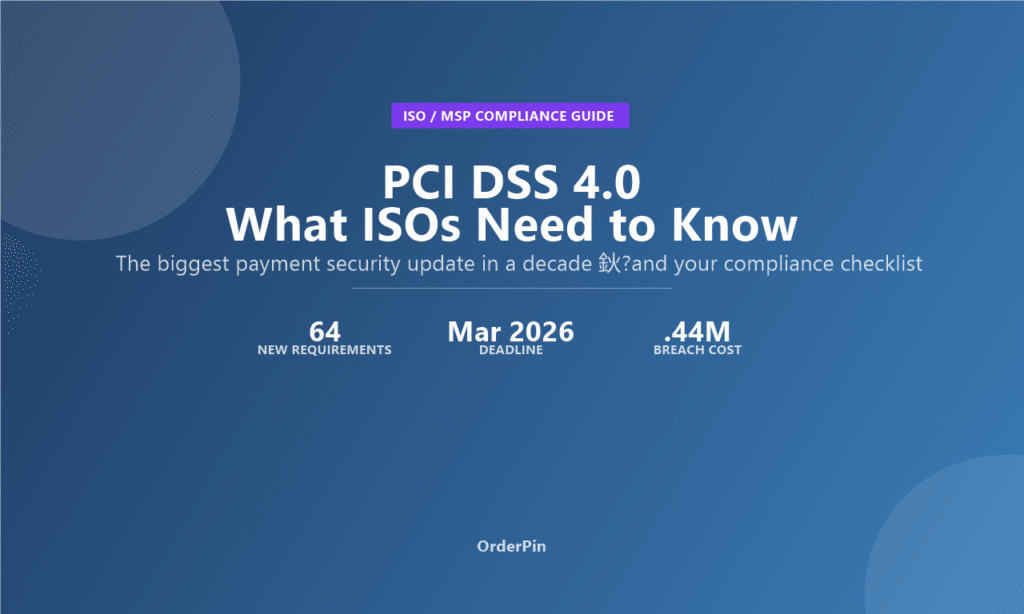
- PCI DSS 4.0 became mandatory on March 31, 2025, replacing v3.2.1 with 64 new or updated requirements — the biggest shift in payment security in a decade.
- 13 requirements were immediately required; the remaining 50+ have until March 31, 2026 to implement, giving ISOs a one-year compliance runway.
- ISOs must update their POS platforms and merchant portfolios to meet multi-factor authentication, targeted risk analysis, and enhanced encryption standards — or face liability exposure.
Last updated: April 2026
What Is PCI DSS 4.0?
PCI DSS 4.0 (Payment Card Industry Data Security Standard version 4.0) is the most significant overhaul of payment card security requirements in over a decade. Published by the PCI Security Standards Council in March 2022 and made mandatory on March 31, 2025, this update replaces PCI DSS v3.2.1 with 64 new or significantly updated requirements spanning authentication, encryption, network security, and vulnerability management. For Independent Sales Organizations (ISOs) and Merchant Service Providers (MSPs) who sell and support POS systems, PCI DSS 4.0 is not optional — it is the compliance floor that determines your liability exposure, your platform’s marketability, and your relationships with acquiring banks and payment processors.
According to the PCI Security Standards Council, the 4.0 update was driven by three forces: the proliferation of sophisticated cyber threats targeting payment data, the expansion of cloud and hybrid infrastructure, and the growing use of multi-channel payment acceptance. The result is a standard that is more prescriptive about how you achieve security — and more flexible about customized implementations that meet the same outcome.
The 13 Requirements Already in Effect (March 2025)
When PCI DSS 4.0 became mandatory on March 31, 2025, 13 requirements were immediately required. These represent the most security-critical updates that the PCI Council deemed urgent enough to not wait for the extended timeline. Understanding these is essential for any ISO advising merchants or evaluating POS platforms.
1. Enhanced Multi-Factor Authentication (MFA) — Requirement 8.4.2
Multi-factor authentication became mandatory for all access into the cardholder data environment (CDE) — not just admin accounts. This includes any user with access to systems that store, process, or transmit cardholder data. For POS resellers, this means your software must support MFA for all backend access, and merchants with older POS systems may need hardware or software upgrades to comply.
2. Targeted Risk Analysis — Requirement 12.3.1
Organizations must now perform a targeted risk analysis to determine the frequency of activities that the standard requires to be performed periodically. Instead of fixed schedules, you must justify the frequency based on your specific risk profile. For ISOs managing multiple merchant portfolios, this means documenting risk assessments for each merchant segment you support.
3. Targeted Risk Analysis for Passwords — Requirement 8.3.9
Password requirements now require risk analysis to determine the appropriate minimum password length — which can be customized based on your security posture rather than a one-size-fits-all minimum. However, NIST guidelines increasingly recommend passphrases of 15+ characters as more secure than complex short passwords.
4. System Component Inventory — Requirement 2.4.1
Organizations must maintain an inventory of system components in scope for PCI DSS. This extends beyond hardware to include software, firmware, and cloud services. For white-label POS providers, this means your entire technology stack — from payment gateway to front-end software — must be documented and kept current.
5. Primary Functions and Roles — Requirement 6.4.3
All running services, protocols, and ports on systems in the CDE must be identified and documented, along with their business justification. This is critical for POS systems where numerous background services often run without documentation.
6. Data Protection Methods — Requirement 3.3.2
Account data stored on magnetic stripe chips or CVV data must be protected using strong cryptography. This requirement impacts any POS system that temporarily stores card reader data.
7. Authentication Policies — Requirement 8.4.1
Strong passwords, MFA, and authentication policies must be documented and enforced. This includes requirements around password changes, lockout thresholds, and session timeouts.
8. Shared Authentication Data Prohibition — Requirement 8.4.2
Individual user IDs and passwords are now strictly required. Shared or generic accounts in the CDE are prohibited unless individually assigned and documented with a business justification.
9-13. Additional Immediate Requirements
The remaining five immediate requirements cover: automated technical solutions for vulnerability scans (Req 11.4.7), scripting language controls on payment pages (Req 6.4.2), phishing protections for personnel (Req 5.4.1), personalized security awareness training (Req 12.6.3), and multi-factor authentication for all access to the CDE (Req 8.4.2 expanded scope).
The 50+ Requirements Coming March 31, 2026
The bulk of PCI DSS 4.0 requirements — over 50 — have an extended implementation deadline of March 31, 2026. These represent more complex architectural changes, broader scope, and deeper integration requirements. Below are the categories most relevant to ISOs and POS platform providers:
Network Security Updates
Requirement 11.6.1 mandates change and intrusion detection for payment pages and payment application endpoints. This is particularly significant for cloud-based POS platforms and any ISO offering web-based payment portals. Automated monitoring tools must detect unauthorized modifications to HTTP headers and script modifications on payment pages.
Enhanced Encryption Standards
Requirements around strong cryptography for account data in transit are being expanded. TLS 1.2 or higher is now mandatory for all cardholder data transmission. Older POS systems still running TLS 1.0/1.1 must be upgraded or replaced.
Expanded Scope for Cloud Environments
PCI DSS 4.0 introduces more specific requirements for cloud-based payment environments, including responsibilities for both cloud service providers and customers. For white-label POS platforms running on cloud infrastructure, this means clearer documentation of security responsibilities and shared compliance models.
Customized Implementation
One of the most significant changes in PCI DSS 4.0 is the introduction of the Customized Approach — an alternative to the traditional prescriptive requirements that allows organizations to meet the intent of a requirement through alternative security measures, as long as they are validated by an independent assessor. This provides flexibility for sophisticated POS providers but requires extensive documentation and compensating controls.
How PCI DSS 4.0 Impacts Your ISO Business
For ISOs and MSPs, PCI DSS 4.0 compliance is not just about your own internal systems — it affects your entire merchant portfolio, your POS platform selection, and your liability exposure with acquiring banks.
Why PCI DSS 4.0 Matters for Your ISO Business
1. Platform Compliance Becomes a Sales Requirement
As PCI DSS 4.0 becomes the baseline for all payment processing, merchants will increasingly ask about your platform’s compliance status before signing contracts. Enterprise merchants, restaurant chains, and high-volume retailers often require a PCI DSS Attestation of Compliance (AOC) as part of their vendor vetting process. If your white-label POS platform cannot provide this, you lose deals.
2. Merchant Portfolio Compliance Monitoring
Many ISOs are surprised to learn that their own compliance status can be impacted by the merchants in their portfolio. While PCI DSS compliance is technically the merchant’s responsibility, ISOs who recommend or provide non-compliant POS systems can face liability. A proactive ISO will help merchants understand their compliance requirements and provide compliant solutions.
3. The Cost of Non-Compliance
While PCI DSS itself does not impose financial penalties (those come from payment brands), the consequences of non-compliance are severe: data breaches costing an average of $9.44 million per incident in the U.S. (IBM, 2024), potential termination of payment processing relationships, and reputational damage that can destroy an ISO’s book of business overnight.
4. Upgrading Non-Compliant POS Systems
Merchants running older POS systems that cannot be upgraded to meet PCI DSS 4.0 requirements face a difficult choice: upgrade or face increased liability. For ISOs, this creates an opportunity — proactively offering compliant POS upgrades to your merchant base before compliance deadlines creates trust, reduces churn, and opens conversations about expanding services.
How to Check if Your POS Platform Is PCI DSS 4.0 Compliant
Before recommending a white-label POS platform to your merchant base, verify its compliance status using these steps:
- Request the AOC: Ask the platform provider for a current Attestation of Compliance. The AOC should clearly state the PCI DSS version (4.0) and the assessment date.
- Check the assessment date: PCI DSS assessments are valid for one year. Make sure the AOC is current and not expired.
- Review the scope: Understand which components are covered in the compliance assessment. Cloud-hosted platforms should include all infrastructure components.
- Verify the QSA: The assessment should be conducted by a qualified security assessor (QSA) or internal security assessor (ISA) approved by the PCI Council.
- Check for compensating controls: If the platform uses compensating controls for any requirements, understand what they are and whether they adequately address the security risk.
What OrderPin Provides for ISO Partners
OrderPin’s white-label POS platform was built from the ground up with modern security standards in mind, making the transition to PCI DSS 4.0 straightforward for ISO partners. Here’s how OrderPin supports your compliance needs:
Why ISO Partners Choose OrderPin
Frequently Asked Questions
What is the difference between PCI DSS 3.2.1 and 4.0?
PCI DSS 4.0 introduces 64 new or significantly updated requirements compared to v3.2.1, with a focus on multi-factor authentication, targeted risk analysis, enhanced encryption, and cloud security. The most significant change is the shift from prescriptive requirements to a more flexible outcome-based approach, including the new Customized Implementation option.
What happens if my ISO business does not comply with PCI DSS 4.0?
While the PCI Council does not impose fines directly, non-compliance can result in increased liability in the event of a data breach, with average U.S. breach costs of $9.44 million (IBM, 2024). Additionally, payment brands and acquiring banks can impose fines on non-compliant merchants and ISOs, and processors may terminate relationships with non-compliant ISO partners.
Can ISOs use a white-label POS platform to meet PCI DSS 4.0 requirements for their merchants?
Yes. ISOs can resell white-label POS platforms that are themselves PCI DSS 4.0 compliant, which transfers the technical compliance burden to the platform provider. ISOs are still responsible for ensuring their merchants use the platform correctly and maintain their own compliance within their portion of the cardholder data environment.
Does PCI DSS 4.0 apply to cloud-based POS systems?
Yes. PCI DSS 4.0 significantly expanded its guidance for cloud environments, including clearer requirements for shared responsibility models between cloud providers and customers. Cloud-based POS platforms like OrderPin must include all cloud infrastructure components in their PCI DSS compliance scope and provide documentation of the shared security responsibilities.
What is the PCI DSS 4.0 compliance deadline for existing systems?
The 13 immediately required best practices became mandatory on March 31, 2025. The remaining 50+ requirements have a grace period until March 31, 2026. After March 31, 2026, all PCI DSS assessments will be against version 4.0, and v3.2.1 will no longer be accepted as a valid standard.
Conclusion
PCI DSS 4.0 represents a fundamental shift in payment security standards — from checklist compliance to risk-based, outcome-driven security. For ISOs and MSPs, the message is clear: the window to upgrade non-compliant POS platforms and align with compliant white-label providers is closing. With the March 31, 2026 deadline for 50+ additional requirements approaching, ISOs who act now will protect their merchant portfolios, strengthen their processor relationships, and position themselves as trusted security advisors rather than just POS vendors.
The good news: choosing a PCI DSS 4.0-ready white-label POS platform like OrderPin removes the heavy lifting of compliance from your shoulders. With built-in MFA, TLS 1.3 encryption, full AOC documentation, and cloud-native security architecture, OrderPin lets you sell with confidence — and sleep better at night.
About OrderPin
OrderPin is a white-label POS platform built for ISO and MSP partners. We offer full data ownership, flexible pricing, and seamless API integrations to help you build a recurring revenue business under your own brand. Our platform is designed with PCI DSS 4.0 compliance built in from day one.
Learn more about OrderPin’s white-label solution